Tagged in
Information Security
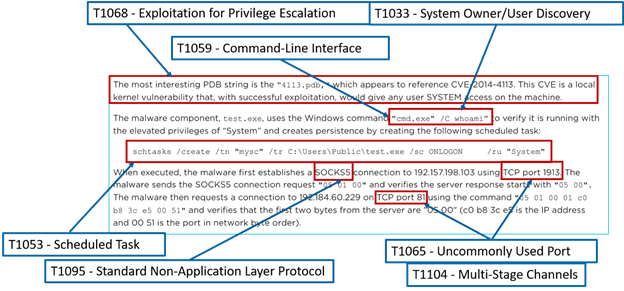
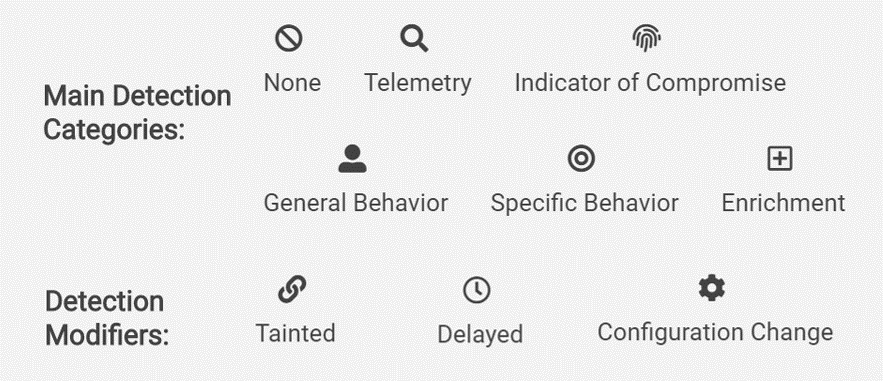
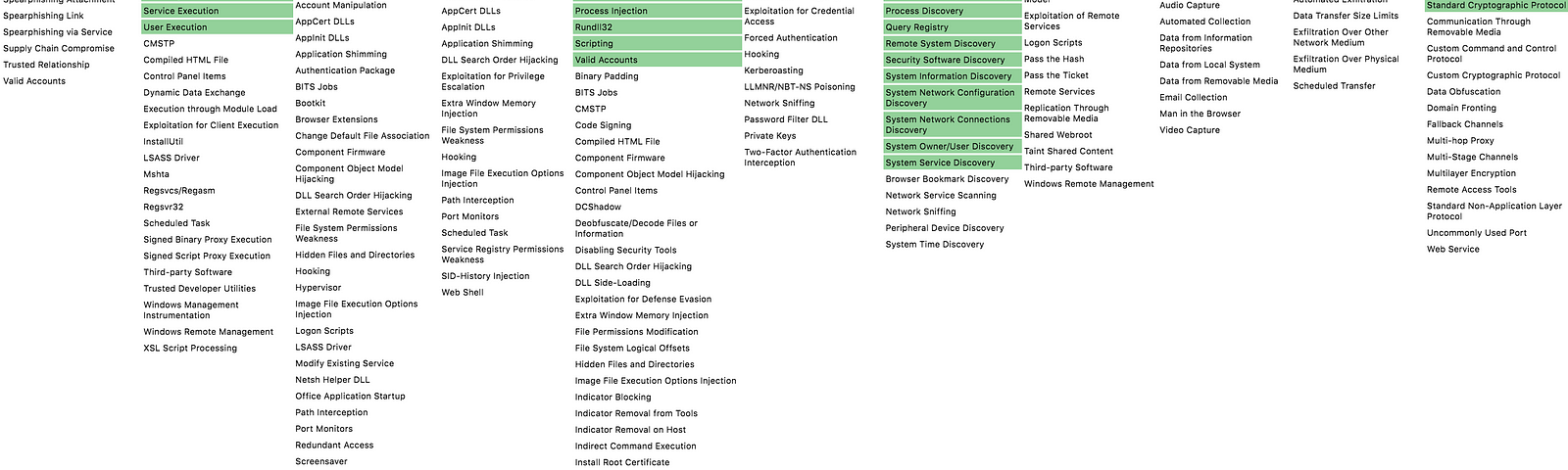
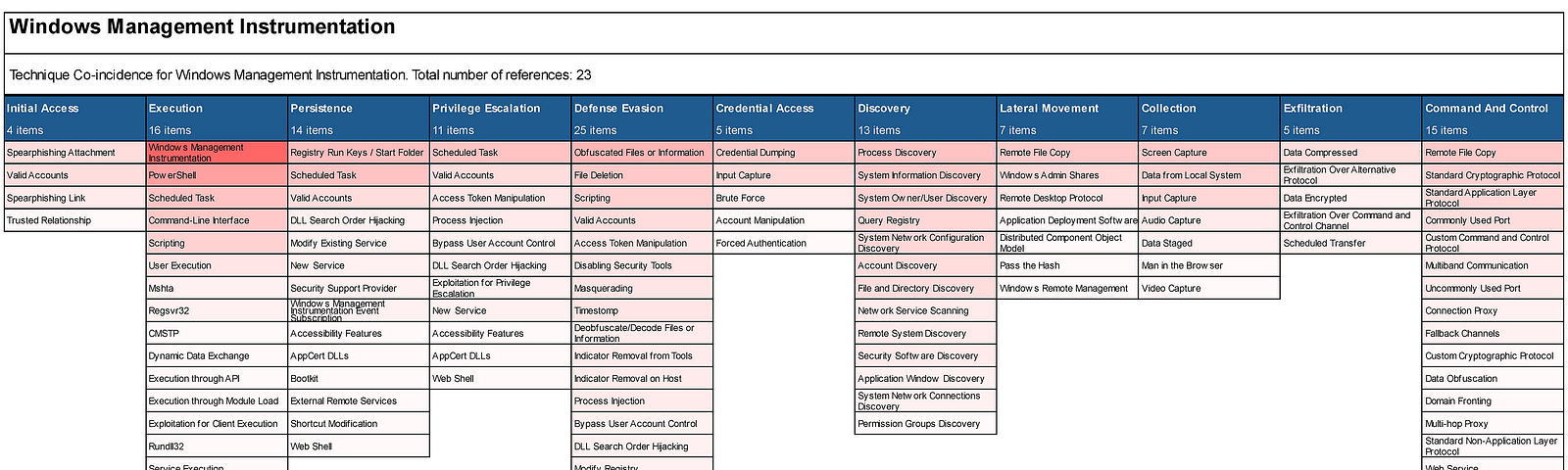
MITRE ATT&CK®
This is the official blog for MITRE ATT&CK®, the MITRE-developed, globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. The full website is located at https://attack.mitre.org.
More informationFollowers
More, on Medium