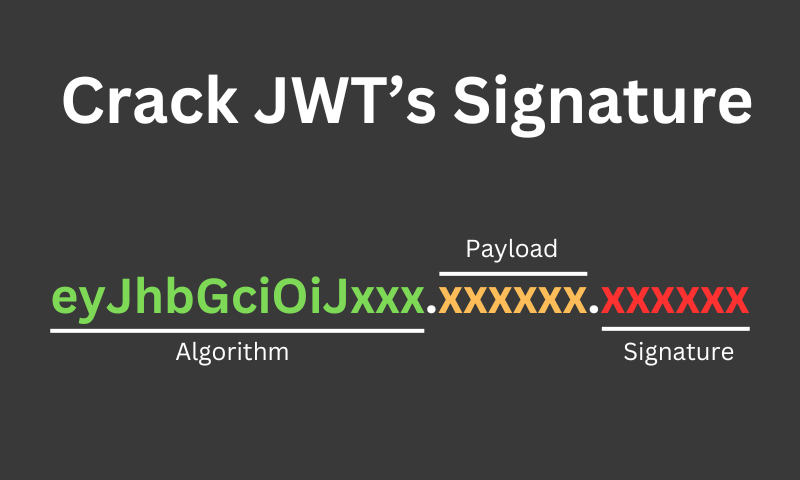
Crack JWT (Secret Key) using Hashcat
When doing pentests, we often find web applications that implement JSON Web Tokens (JWT). JWT…
These were the top 10 stories published by MII Cyber Security Consulting Services in March of 2024. You can also dive into daily archives for March of 2024 by using the calendar at the top of this page.